~hackernoon | Bookmarks (2034)
-
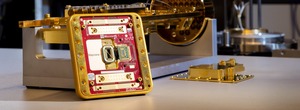
Google, Microsoft, and IBM Are Fighting for Quantum Supremacy—Here’s Who’s Winning
While the world fixates on AI, a far more consequential technological battle unfolds in specialized labs...
-
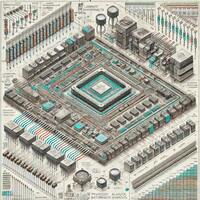
How FPGA-based Digital Quantum Coprocessors Work
FPGA-based digital quantum coprocessors is a middle-ground between classical and quantum computing.
-
The Future of Database Administration Is Evolution, Not Extinction
Database administration is evolving rapidly as AI technologies mature. Integrating AI-driven automation and intelligent analytics into...
-
Anti-dog Meme Advocate Says he Refuses to Fall Into the Rabbit Hole of Shooting to the Moon
Catswithouthats is an anti-dog meme advocate and gonzo economist. He is working on a project developing...
-
What Makes an NFT Project Worthwhile?
Researchers selected 18 significant NFT profile picture projects, including CryptoPunks and BAYC, based on their impact,...
-
Stop Fighting Data Sync Issues—This Guide Makes MySQL-to-PostgreSQL Transfers Easy
This article provides a detailed walkthrough of how to achieve full data synchronization from MySQL to...
-
Stop Wasting Time on Broken Data Syncs—Here’s How to Do It Right with Apache SeaTunnel
In this guide, we will walk you through a lightweight data migration and synchronization solution from...
-
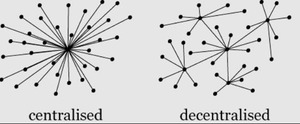
Amazon and Microsoft Don’t Want You to Know About This Cloud Alternative
The key to mainstream adoption of decentralized cloud solutions is framing them around user benefits rather...
-
Hospitals Are Now Considering Using AI to Keep Patients Safe
Artificial intelligence (AI) has become an essential part of many industries. It can enhance practices, streamline...
-
How Social Media Shapes Buying Behavior
Social media, especially Twitter, plays a key role in online engagement, product adoption, and market prediction....
-
Rollups Are the Future—But Their Biggest Bottleneck Might Be a Single Point of Failure
For all the innovation that rollups bring, they still carry a significant centralization risk.
-
6 Of The Best Google Review Management Software Tools In 2025, Tried & Tested
Localo is the best Google review management software in 2025. It lets you reply to reviews...
-
“Winning and Losing is Often in the Details.” Ritesh Lad on the Art of High-stakes Proposal Writing
Winning proposals are more than just documents—they’re strategic business tools. Ritesh Lad, a Senior Proposal Writer...
-
Stop Moving Data Manually—Let DolphinScheduler’s Output Variables Do the Heavy Lifting For You
Master output variables in ApacheDolphinScheduler to boost workflow flexibility! Learn how to use task-specific & workflow-level...
-
Vibe Coding Will 10X Every Developer, Yet Never, Ever, Replace Them
Vibe coding will make every developer a 10X developer. And it will make existing 10X developers...
-
Remember When NFTs Were All the Rave on Twitter?
This research examines Twitter’s role in the NFT ecosystem, focusing on profile picture projects like Bored...
-
Will Xandeum’s pNodes Unlock Solana’s True Potential?
Xandeum launches pNodes on Solana devnet, a scalable storage solution for smart contracts. Learn how it...
-
Can Blockchain and AI Finally Trust Each Other? Flare and Google Cloud’s Hackathon Says Yes
Explore how the Flare x Google Cloud Hackathon (March 7-9, 2025) united blockchain and AI. Over...
-
How Multi-Agent Systems Are Rethinking LLM Architecture
Large Language Models (LLMs) are capable of incredible feats in terms of natural language processing. But...
-
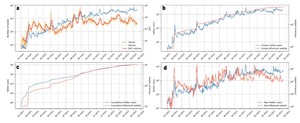
ChatGPT's Macroeconomic Predictions
GPT-4’s predictions for inflation and unemployment improve with future narrative prompts. This section presents data showing...
-
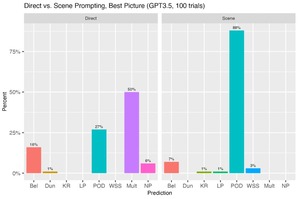
How Future Narratives Improve ChatGPT’s Oscars Predictions
GPT-4’s Academy Award predictions improve significantly when using future narrative prompts instead of direct predictions. This...
-
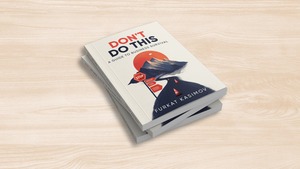
Furkat Kasimov Unveils Business Secrets in Entrepreneurial Success through Upcoming Book
Don't Do This: A Guide to Business Survival," offers a sobering look at what it takes...
-
The Best Auto-Retweet Tools to Keep Your X Account Active
Keeping your Twitter account active and engaging requires constant effort, but not everyone has the time...
-
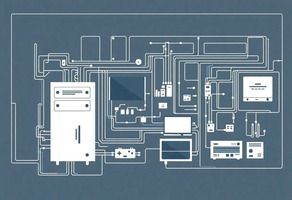
A Senior Engineer’s Guide to Scalable & Reliable System Design
System design refers to the process of defining and creating a high-level architecture that meets certain...