~hackernoon | Bookmarks (2041)
-
TSJ Diversified Group, Smart Mountain, Self-employed in Austria: HackerNoon Startups of The Week
Welcome to HackerNoon Startups of the Week! Each week, the HackerNoon team showcases a list of...
-
Can Blockchain Make AI Systems More Transparent? Share Your Thoughts to Win From $2000
Join the #blockchain Writing Contest and share your insights on decentralized AI, cloud, or dePIN. Win...
-
Mawari Pioneers City-Wide AI Experience in Osaka’s Namba District: How Osaka is Entering the Future
Discover how Mawari is spearheading Osaka’s digital evolution with Digital Entertainment City Namba—a city-wide integration of...
-
Here's How the Pros Choose the Right Load Balancer
Load balancers distribute traffic across multiple servers to enhance performance, prevent downtime, and optimize resource usage....
-
Heroku Now Officially Supports .NET!
.NET developers now have access to the officially supported buildpack for .NET, which means you can...
-
Statutory Boards Represent Legacy Systems That Have Outlived Their Purpose
With the enactment of the Public Enterprises Act, we've created a redundant layer of bureaucracy that...
-
Goodbye, Compute-Hungry Models—This Tiny AI Is the Future of Prediction
Researchers have developed a practical, efficient alternative to massive AI models for time series forecasting.
-
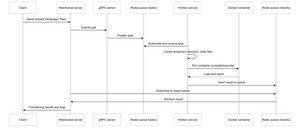
This Web IDE Runs Your Code in the Cloud—Without Melting Your Laptop
The project is built on the principle of microservice architecture, which allows you to divide functionality...
-
Big AI Models Are Struggling—This Tiny One Wins With 45% More Accuracy
Researchers have developed a practical, efficient alternative to massive AI models for time series forecasting.
-
Love & Friendship 2.0: Communications Apps Are Changing the Game
Long-distance romances and meaningful friendships are established entirely via online communication platforms. With the value of...
-
Experimenting With Helm Can Take Your Kubernetes Skills to the Next Level
Helm is a package manager for Kubernetes that helps deploy, configure and manage applications in a...
-
This AI Model Learns to Forecast With Almost No Training—Here’s How
Researchers have developed a practical, efficient alternative to massive AI models for time series forecasting.
-
Are China and the U.S. Engaged in a Race Toward AI Armageddon?
The race between China and the U.S. to dominate artificial intelligence (AI) is not just about...
-
A New Tiny AI Model Is Outsmarting the Big Guys With a Four-Part Brain
Researchers have developed a practical, efficient alternative to massive AI models for time series forecasting.
-
NFT Paris 2025 Review: An Amazing Event, But Onboarding Normies? We’ve Got Work to Do
NFT Paris 2025 brought community and innovation to life, but onboarding struggles show Web3 still has...
-
IBM Researchers Create Mini AI Model That Predicts the Future
Researchers have developed a practical, efficient alternative to massive AI models for time series forecasting.
-
Reducing Server and Database Costs by 50% for an Insurance Broker using AWS
Hosting all services in a single public cloud and relying solely on credential protection can cause...
-
GraphQL is a Misunderstood Framework
GraphQL is an often misunderstood framework that went from being one of the most popular development...
-
Microsoft Researchers Identify 8 Core Security Lessons for AI
Microsoft AI Red Team releases whitepaper detailing lessons from its 100 generative AI products. Security researchers...
-
Mastering Response Compression Middleware in ASP.NET Core
This guide offers a comprehensive walkthrough of response compression in ASP.NET Core. It explores what is...
-
The HackerNoon Newsletter: How to Fit an Elephant in a Spreadsheet (2/20/2025)
How are you, hacker? 🪐 What’s happening in tech today, February 20, 2025? The HackerNoon Newsletter...
-
How to Build a No-Limits Stock Market Scraper with Python
Traditional stock market APIs come with rate limits and high costs, so I built my own...
-
Apex Fusion Launches PRIME Chain and AP3X Token, Bridging Bitcoin and Ethereum
Apex Fusion has launched its blockchain ecosystem with the AP3X token and PRIME chain, aiming to...
-
Why Crypto’s Future Depends on Fair and Transparent Token Distribution
Berachain’s BERA token launch has reignited debates over fair vs. VC-backed token distributions, as insiders dumped...