~hackernoon | Bookmarks (2041)
-
UI/UX Designer Ahmed Adel Says He Wished He Had Invested in Ergonomics
As a Senior UI/UX Designer and Design Lead at Edgy Labs, Ahmed Adel focuses on creating...
-
This One Programming Choice Completely Changed These Tech Firms—Here's How
Clojure is reshaping how teams build software, enabling small, focused groups to tackle complex challenges efficiently....
-
Competition Between WordPress Page Builders Is Heating Up
WordPress has evolved significantly since its early days as a simple blogging platform.
-
These 2 AI Agent Frameworks Appear to Be Dominating Headlines—But Which One's Better?
While Eliza and GAME are rather distinct AI agent frameworks with different applications, they both integrate...
-
Build a Monster-Finding Tool For Your Next D&D Session That Picks the Right Encounter For You
The article explores multi-attribute vector search, comparing two key approaches. The naive method involves storing each...
-
This Open Source Networking Protocol Is Actually Better At Handling Connectivity
FreeRADIUS and RADIUS infrastructure enable secure and efficient authentication, authorization, and accounting (**AAA**) processes for seamless...
-
The TechBeat: Silicon Valley Is In the Midst of an Ideological Battle That Nobody is Talking About (1/31/2025)
How are you, hacker? 🪐Want to know what's trending right now?: The Techbeat by HackerNoon has...
-
-
Defining Temporal Hierarchies and How We Proved That Corresponding Hierarchies Are Always Strict
We defined temporal hierarchies using the unary temporal logic operator C 7→ TL(C). We looked at...
-
The HackerNoon Newsletter: Profit-hungry Corporations Own Your Most Intimate Data (1/30/2025)
How are you, hacker? 🪐 What’s happening in tech today, January 30, 2025? The HackerNoon Newsletter...
-
HackerNoon Decoded 2024: Celebrating Our Management Community!
Welcome to HackerNoon Decoded—the ultimate recap of the Management stories, writers, and trends that defined 2024!...
-
Design Shifts at HackerNoon: Streamlined Top Nav, Quick Search and Settings Dashboard 🚀
HackerNoon has just rolled out a major update to its design. The new design includes a...
-
Profit-hungry Corporations Own Your Most Intimate Data
In 2025, we shouldn't be trusting our bodies' most intimate data to closed systems run by...
-
Meet COOCO, The BD School, and ClikinTech: HackerNoon Startups of The Week
Welcome to HackerNoon Startups of the Week! Each week, the HackerNoon team highlights standout Startups from...
-
Designing the Future: A UI/UX Journey with Roman Shimin
A UX/UI Design Lead at Appello shares their journey, rapid design workflows, favorite tools, and career...
-
EigenLayer and Cartesi Launch Initiative to Build Mainstream Blockchain Use Cases for User Adoption
EigenLayer and Cartesi collaborate to develop new blockchain use cases, focusing on AI, DeFi, gaming, and...
-
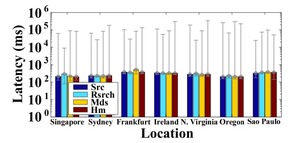
Evaluating Multi-Cloud Event Distribution and Load Balancing in DeFaaS
The evaluation highlights the impact of geographical location over cloud provider on multi-cloud event latency, and...
-
Here's How to Keep Tempdb From Becoming Your Worst Nightmare
To tackle `tempdb` issues in SQL Server, start by checking current space usage with `sys.database_files` and...
-
Your Machine Learning Model Doesn’t Need a Server Anymore
Serverless AI/ML pipelines automate scalable data processing and model deployment without infrastructure management.
-
A 2021 Hackathon Project Pitched Blockchain Internet. It Sounded Crazy—Until Now
The Satellite Broadband Service Chain, recognized as a Top Quality Project Winner during the Chainlink Fall...
-
How DeFaaS Makes Cloud Functions Work Across Multiple Providers
DeFaaS utilizes Hyperledger Besu and OpenFaaS on Kubernetes, integrated with IPFS for decentralized event distribution. The...
-
Hybrid Work is Frustrating—Here's What Employers Can Do Instead
The key to successful RTO is see it from a difference lens — to make it...
-
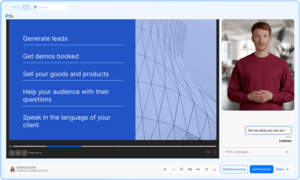
Pitch Avatar Launches AI-powered Chat Avatar for Seamless Business Communication
Combining advanced conversational AI with dynamic visuals, Chat-avatar empowers businesses to engage clients, employees, and partners...
-
What Makes DeFaaS a Game Changer in Multi-Cloud Service Coordination?
DeFaaS employs decentralized logging through IPFS, asynchronous billing via blockchain, and trust management mechanisms such as...