~hackernoon | Bookmarks (2034)
-
The HackerNoon Newsletter: Lumoz Unveils TEE+ZK Multi-Proof for On-chain AI Agent (1/19/2025)
How are you, hacker? 🪐 What’s happening in tech today, January 19, 2025? The HackerNoon Newsletter...
-
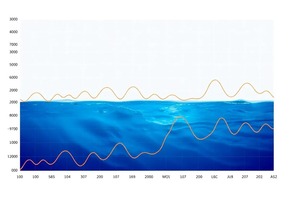
DeepSee: Making It Easier to Analyze and Explore Ocean Data for Future Research
DeepSee enables groundbreaking multidimensional visualizations of seabed sediment cores, offering new ways to predict and explore...
-
Meta's Superapp Ambitions Take Shape as WhatsApp Expands UPI Access in India
India is considered WhatsApp’s largest market, with hundreds of millions of monthly active users. WhatsApp Pay...
-
GameGPT Launches Genesis AI NFT Collection, Combining AI And Blockchain For The Future Of Gaming
GameGPT launches Genesis AI NFT Collection of 6,000 NFTs. NFT owners can upgrade digital assets into...
-
How to Boost App Downloads with AI-Powered Promo Videos
Learn how to create professional app promotional videos using AI tools like Similarvideo. This guide covers...
-
The TechBeat: Project DIGITS: NVIDIA’s Leap into Personal AI Supercomputing (1/19/2025)
How are you, hacker? 🪐Want to know what's trending right now?: The Techbeat by HackerNoon has...
-
How DeepSee Is Changing the Way Scientists Use Data in the Field
DeepSee’s deployment revealed critical lessons, including the need to prioritize data integration, visualize data in environmental...
-
The HackerNoon Newsletter: Master Manipulators: 5 Behaviors to Watch Out For (1/18/2025)
How are you, hacker? 🪐 What’s happening in tech today, January 18, 2025? The HackerNoon Newsletter...
-
What Needs Improvement in DeepSee for Ocean Research? Experts Weigh In
Experts discussed several limitations of DeepSee, including challenges with data formatting, accuracy of interpolation methods, and...
-
Polkadot Rollup, Hyperbridge, Extends Initial Relayer Offering After Selling Over 52 Million Tokens
Hyperbridge announces extension of Initial Relayer Offering deadline. Over 52 million tokens out of total 100...
-
The TechBeat: A Peek Into BlueSky's AT Protocol Helped Me Understand Why It Needs to Exist (1/18/2025)
How are you, hacker? 🪐Want to know what's trending right now?: The Techbeat by HackerNoon has...
-
Bridging Computational Notions of Depth: Working Towards the Proof of Lemma 3
Working towards the proof of Lemma 3, we first establish the following result.
-
Attention Hackers - Work on Yourself
Hackers are particularly good at one thing: Hacking. But hackers are particularly bad at another thing:...
-
How to Build Backends Lightning-Fast With YAML: Digesto
Digesto is an experimental Node.js library that lets you define your data model in a YAML...
-
A Guide to Moving, Copying, or Sharing ChatGPT Conversations
AI enthusiast couldn't log on to OpenAI's ChatGPT.com. He tried all sorts of ways to fix...
-
Synchronization Challenges in Multithreading
This is the sixth part of a series on Parallel Programming for Beginners. In this article,...
-
The Importance of Data Quality Management and Data Integration for AI Models
Data Quality Management (DQM). It’s on top of many businesses’ minds. In this AI generation, quality...
-
36 UX Tips (and Pitfalls) for B2B2C Product Managers
B2B2C is where your platform (the B2B component) serves businesses who, in turn, serve end consumers....
-
EIP-7623: The Proposal That Will Re-price Calldata For Ethereum Transactions
EIP-7623 proposes changes to Ethereum's calldata pricing structure, aiming to make gas costs more reflective of...
-
How Computers Are Designed for Extreme Environments
Not every device can operate in every environment; once engineers know the usage environment, they can...
-
Earth’s Aerial Biosphere Offers Insights into Venusian Microbial Survival
Earth's aerial biosphere supports transient microbial life in clouds, contrasting Venus' potential for permanent microbial habitation...
-
Microbial Life on Venus Requires a Unique Life Cycle to Overcome Extreme Conditions
This study revisits the potential for life in Venusian clouds, addressing challenges like acidity, low water...
-
Researchers Proposes a Life Cycle for Venusian Microbes
The authors propose a life cycle for Venusian microbes that begins in the lower haze layer...
-
Life in Venusian Clouds: A Hypothesis for Microbial Survival and Life Cycle
This research proposes a life cycle for microbial survival in Venus' atmosphere, addressing challenges of persistence....