~hackernoon | Bookmarks (2041)
-
How DeepSee Helped Ocean Researchers Make Smarter Decisions During Their Expedition
DeepSee was deployed during a Gulf of California expedition to aid in ocean research data organization,...
-
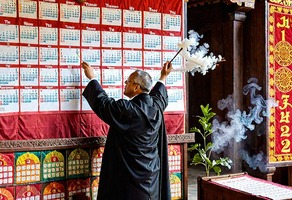
Honor Your Red Letter Days and Keep them Holy
Red Letter Days are key dates that hold cultural, emotional, or historical significance. By aligning your...
-
Why JWT Is the Key to Securing Your Enterprise App – And Why KumuluzEE Might Be Your New Best Friend
'JWT' or JavaScript Object Notation Web Token is a standard defined in [ RFC7519] It can...
-
Is Developing Blockchain as a Backend Really All That Hard?
This article isn’t about cryptocurrency or decentralized finance. Instead, we’ll explore public EVM blockchains and how...
-
Gamification Boosts Software Testing—Until the Rewards Run Out
Researchers in Spain have found that gamification is better at motivating software engineering students in performing...
-
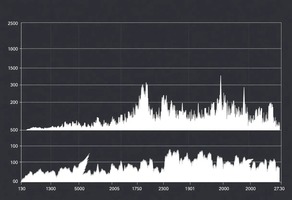
HackerNoon Decoded: The Polls that Defined 2024
As 2024 draws to a close, it’s time to reflect on the key moments that shaped...
-
The Hidden Pitfalls of Gamification in Software Testing
Researchers in Spain have found that gamification is better at motivating software engineering students in performing...
-
How Far Can Gamification Take Software Testing?
Researchers in Spain have found that gamification is better at motivating software engineering students in performing...
-
A New Frontend Hack Is Changing API Performance For the Better
In the past, developers used the same API for both reads and writes on every case....
-
Researchers Say Gamified Learning Boosts Student Engagement and Performance in Software Testing
Researchers in Spain have found that gamification is better at motivating software engineering students in performing...
-
A Semester-Long Experiment Shows Gamification Boosts Learning Outcomes in Software Testing Education
Researchers in Spain have found that gamification is better at motivating software engineering students in performing...
-
Did You Know Trees Feel the Pull of the Moon? Scientists Link Sap Flow to Lunar Tides
A new paper investigates the intriguing possibility that gravitational forces from celestial bodies influence electrical activity...
-
NFT Transaction Networks Are Highly Decentralized and Influenced by Key Nodes
This section examines NFT transaction networks using graph analysis, revealing decentralized structures and key influential nodes....
-
Dataset Exploration and Experimentation for NFT Transaction Analysis
This section focuses on datasets and tools used for NFT transaction analysis on the Ethereum blockchain....
-
Understanding NFT Transaction Networks Through Analysis and Prediction
This paper analyzes NFT transaction networks on Ethereum, focusing on growth, influential nodes, and market trends....
-
Graph Analysis and Bubble Prediction Are Key to Understanding NFT Networks
This section reviews prior work on blockchain graph analysis, focusing on ERC-20 and ERC-721 token networks...
-
NFT Ownership Is Decentralized and Follows a Zipfian Distribution
This methodology section explores NFT ownership trends and decentralized dynamics, revealing that most owners hold few...
-
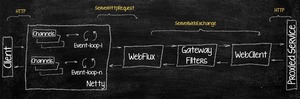
A Single Point of Access or Chaos — Unlocking Non-Blocking API Gateways
Spring Cloud Gateway is a modern, non-blocking API gateway that offers significant improvements over its predecessor,...
-
Solve Concurrency Challenges with Spring's @Transactional Annotation
The article discusses the effective use of the @Transactional annotation in Spring, focusing on solving concurrency...
-
DMCC and REIT Development Unveil Landmark Crypto Tower In JLT
DMCC and REIT Development announce construction of 17-storey Crypto Tower. Tower to support DMCC’s rapidly growing...
-
The HackerNoon Newsletter: To Sell Software in 2025, Devs Must Think Like Marketers (1/16/2025)
How are you, hacker? 🪐 What’s happening in tech today, January 16, 2025? The HackerNoon Newsletter...
-
Trump, Don’t Just Lock Away Your 1 Million Bitcoin—Build a Tech Metropolis Instead
Bitcoin has good SoV and MoE functions. But it needs a semblance of intrinsic value. To...
-
HackerNoon Decoded: The Top 10 Countries Where HackerNoon Is the Most Active
1. United States 2. India 3. China 4. United Kingdom 5. Japan 6. Germany 7. Brazil...
-
Maths Education is Broken—Here’s How We Can Fix It
Dr Sabine’s new video is a logical tome, and I couldn’t quite grasp it. Meanwhile, I...